Most people assume blockchain networks are vulnerable when user access compromise causes most crypto losses. The reality is simpler and more controllable. Your digital assets remain secure when you protect the access points: wallets, private keys, and exchange accounts. This guide walks you through essential crypto security practices in 2026, from safeguarding recovery phrases to choosing the right wallet type. You’ll learn how to defend against phishing, implement strong authentication, and verify transactions before sending funds. Whether you’re new to cryptocurrency or managing a growing portfolio, these fundamentals help you take control of your digital asset security.
Table of Contents
- Understanding Crypto Security Threats And Access Points
- Protecting Wallets, Keys, And Recovery Phrases
- Best Practices For Securing Crypto Accounts And Transactions
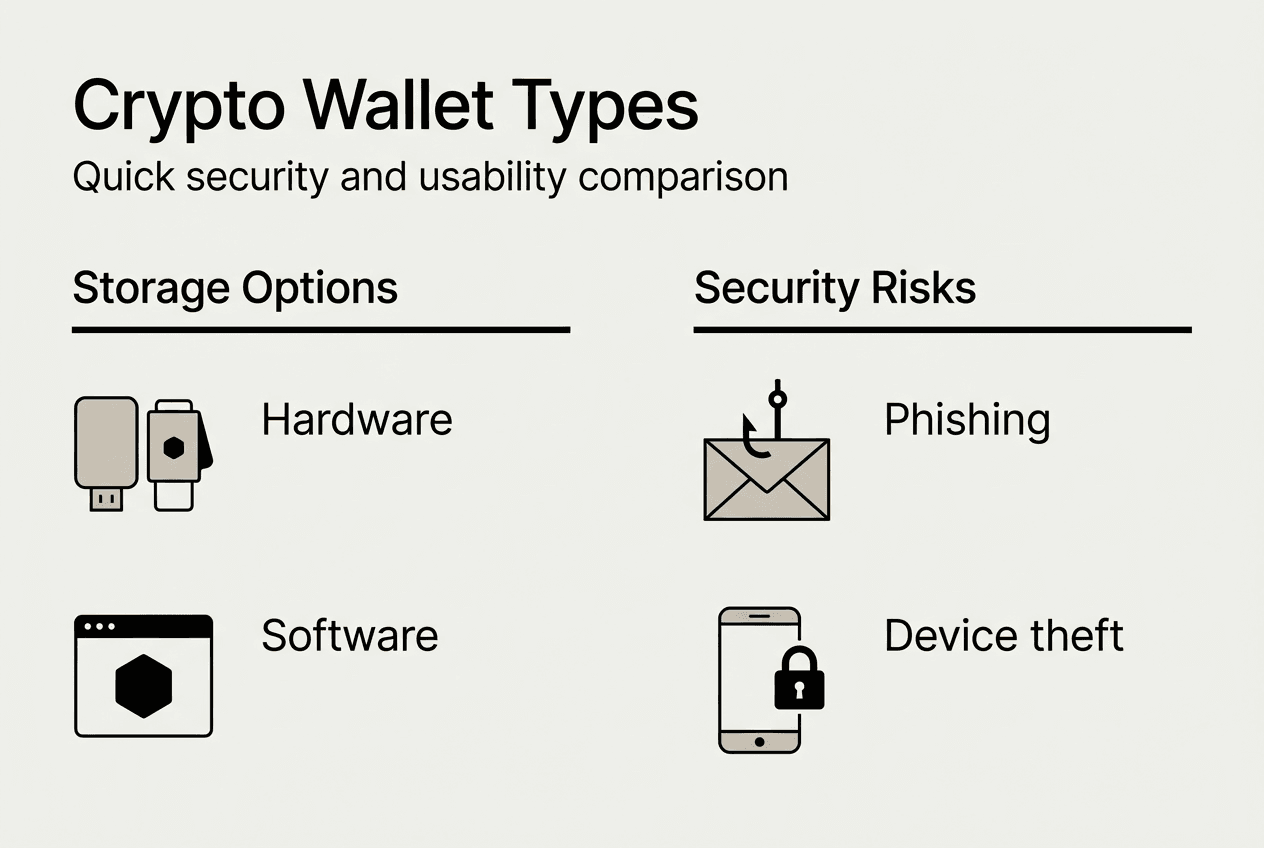
- Understanding Wallet Types And Choosing Safe Storage Methods
- Explore More In Blockchain And Crypto Innovations
Key takeaways
| Point | Details |
|---|---|
| User access is the weak link | Compromised passwords, phishing, and device vulnerabilities cause most crypto losses, not blockchain flaws. |
| Private keys need offline storage | Store recovery phrases and private keys offline using paper, metal backups, or hardware wallets. |
| Authentication layers matter | Enable two-factor authentication and use unique, strong passwords across all crypto accounts. |
| Wallet choice affects control | Custodial wallets trade convenience for third-party trust while personal wallets give you full ownership. |
| Transaction verification prevents errors | Always double-check wallet addresses and amounts before confirming irreversible crypto transfers. |
Understanding crypto security threats and access points
Attackers don’t break blockchain networks. They target you. Your passwords, exchange logins, and wallet access represent the primary vulnerability in crypto security. Understanding these attack vectors helps you build effective defenses against the most common threats facing cryptocurrency holders today.
Phishing remains the top method criminals use to steal credentials. Fake websites mimic legitimate exchanges, tricking users into entering login details or seed phrases. Malware installed on compromised devices captures keystrokes, screenshots, or clipboard data containing wallet addresses and private keys. Social engineering manipulates victims into revealing sensitive information through fake customer support calls or urgent security alerts.
SIM swapping represents a sophisticated attack where criminals convince mobile carriers to transfer your phone number to their device. This bypasses SMS-based two-factor authentication, granting access to accounts protected by text message codes. The scale of these risks is staggering, with cyberattacks resulting in massive financial losses.
Cybersecurity crimes targeting cryptocurrency exchanges resulted in $8.494 billion in losses across 220 incidents between 2009 and 2024.
Your first line of defense involves creating strong, unique passwords for every crypto-related account. Never reuse passwords across platforms. Attackers who breach one service will immediately test those credentials on major exchanges and wallet providers. Use a combination of uppercase and lowercase letters, numbers, and symbols to create passwords that resist brute force attacks.
Verifying website URLs before entering any sensitive information prevents phishing success. Bookmark legitimate exchange sites and wallet interfaces rather than clicking links in emails or messages. Check for HTTPS encryption and examine the domain name carefully for subtle misspellings or character substitutions that signal fake sites.
Staying informed through reliable crypto news sources helps you recognize emerging threats and adapt your security practices. Understanding different types of cryptocurrencies also clarifies which assets require specific security considerations based on their blockchain architecture and wallet compatibility.
Pro Tip: Set calendar reminders to review and update your security practices quarterly, including password changes, software updates, and backup verification.
Protecting wallets, keys, and recovery phrases
Private keys function as the ultimate proof of cryptocurrency ownership. These cryptographic codes authorize transactions from your wallet address. Seed phrases, typically 12 or 24 words, serve as master keys that can restore access to your funds if you lose your device or forget your password. Protecting these credentials represents the foundation of crypto security.
Never store recovery phrases digitally. Screenshots, cloud storage, password managers, and email drafts create attack surfaces for hackers. Write seed phrases on paper or engrave them on metal plates designed for long-term storage. Store these physical backups in secure locations like safes or safety deposit boxes. Consider splitting the phrase across multiple secure locations if the full phrase in one place creates too much risk.
Custodial versus personal wallets present different security tradeoffs. Custodial wallets, offered by exchanges like Coinbase or Kraken, hold your private keys on your behalf. You trust the platform to secure your assets and provide access when needed. Personal wallets, whether software or hardware based, give you complete control over private keys but require you to manage all security responsibilities.
| Wallet Type | Control | Convenience | Security Risk |
|---|---|---|---|
| Custodial | Platform controls keys | High, easy access | Platform breach or failure |
| Personal | You control keys | Medium, requires setup | User error or key loss |
| Cold Storage | You control offline keys | Low, manual process | Physical theft or damage |
Cold wallets store private keys completely offline, eliminating remote hacking risks. Hardware wallets like Ledger or Trezor keep keys isolated from internet-connected devices even when signing transactions. This air gap protection makes cold storage the gold standard for securing significant cryptocurrency holdings.
The importance of protecting your seed phrase cannot be overstated. Anyone with access to your recovery phrase can recreate your wallet on any device and transfer all funds without needing passwords or additional authentication. Treat seed phrases with the same security level as large amounts of cash or valuable documents.
Personal wallet users must balance security with usability. Storing all crypto in cold storage maximizes security but complicates frequent trading or transactions. Many experienced users maintain hot wallets with small amounts for regular use while keeping the majority of holdings in cold storage. This approach limits exposure while maintaining practical access.
Implementing safe investment strategies includes choosing appropriate wallet types based on your holdings and activity level. New users might start with reputable custodial wallets to learn basics before transitioning to personal wallets as their understanding and portfolio grow. Research different types of cryptocurrencies to understand which wallets support your chosen assets.
Pro Tip: Test your recovery phrase backup by restoring a small amount to a new wallet before trusting it with significant funds, then wipe the test device completely.
Best practices for securing crypto accounts and transactions
Strong password hygiene extends beyond complexity. Update passwords regularly, especially after any security incident affecting services you use. Never share passwords with anyone claiming to offer support. Legitimate platforms never ask for passwords, private keys, or seed phrases through any communication channel.
Two-factor authentication adds a critical security layer by requiring a second verification method beyond your password. Even if attackers obtain your password through phishing or data breaches, they cannot access your account without the second factor. Different 2FA methods offer varying security levels and convenience tradeoffs.
| 2FA Method | Security Level | Convenience | Vulnerability |
|---|---|---|---|
| SMS codes | Low | High | SIM swapping |
| Authenticator apps | Medium | Medium | Device theft |
| Hardware keys | High | Low | Physical loss |
Authenticator apps like Google Authenticator or Authy generate time-based codes on your device, eliminating SMS interception risks. Hardware security keys provide the strongest protection by requiring physical possession of the device to complete login. While less convenient, hardware keys effectively prevent remote account takeover attempts.
Transaction verification prevents costly mistakes. Cryptocurrency transactions are irreversible on networks like Bitcoin and Ethereum. Sending funds to the wrong address means permanent loss with no recourse for recovery. Follow this checklist before confirming any transaction:
- Verify the complete recipient wallet address character by character, checking the first and last six characters at minimum.
- Confirm the transaction amount matches your intended transfer, including any network fees.
- Review the cryptocurrency type to ensure you’re sending the correct asset on the right network.
- Test with a small amount first for new recipients or unfamiliar wallet addresses.
- Double-check you’re using the correct blockchain network, as many tokens exist on multiple chains.
Phishing attempts grow more sophisticated each year. Attackers create convincing fake websites, send emails impersonating exchanges, and even purchase ads that appear above legitimate results in search engines. Verify URLs carefully by typing addresses manually rather than clicking links. Check sender email addresses for subtle misspellings or unusual domains.
Common security failures include weak passwords, disabled two-factor authentication, and logging into fake websites that harvest credentials. Avoiding these mistakes requires consistent vigilance and healthy skepticism toward any unexpected communication requesting action on your accounts.
Staying current with crypto news interpretation helps you recognize legitimate platform updates versus social engineering attempts. Following market analysis from trusted sources provides context for understanding whether sudden “urgent” messages align with actual events or represent scam attempts.
Pro Tip: Use a dedicated email address exclusively for crypto accounts, enable advanced security features like login notifications, and maintain a password manager with encrypted storage for complex, unique passwords.
Understanding wallet types and choosing safe storage methods
Wallet categories extend beyond simple custodial versus personal distinctions. Hot wallets maintain constant internet connectivity, enabling quick transactions and easy access. Cold wallets remain offline, prioritizing security over convenience. Non-custodial wallets give you complete control over private keys regardless of whether they’re hot or cold.
Each wallet type serves different use cases and risk profiles. Experienced users prefer personal wallets for the control and security benefits despite increased responsibility. Beginners often start with custodial options to learn basics without risking permanent loss from mishandled private keys.
| Wallet Type | Control Level | Security Risk | Best For |
|---|---|---|---|
| Custodial hot | Platform holds keys | Platform breach | Beginners, small amounts |
| Non-custodial hot | You hold keys | Device compromise | Active traders |
| Non-custodial cold | You hold offline keys | Physical security | Long-term holders |
| Hardware wallet | You hold isolated keys | Device damage or loss | Serious investors |
Choosing appropriate storage methods depends on several factors:
- Portfolio size: Larger holdings justify investing in hardware wallets and more complex security setups.
- Transaction frequency: Active traders need hot wallet access while long-term holders benefit from cold storage.
- Technical comfort: Personal wallets require understanding backup procedures and recovery processes.
- Risk tolerance: Some users accept custodial risks for convenience while others prioritize absolute control.
- Asset diversity: Different cryptocurrencies may require specific wallet types based on blockchain compatibility.
Diversifying storage methods reduces risk concentration. Storing all funds in a single wallet creates a single point of failure. Trusted custodians and cold wallets each play roles in a balanced security strategy. Consider maintaining three tiers: a small hot wallet for regular transactions, a larger warm wallet for medium-term holdings, and cold storage for the bulk of your portfolio.
Hardware wallets bridge security and usability by keeping private keys on specialized devices that never expose them to internet-connected computers. When signing transactions, the hardware wallet displays details on its screen for verification before authorizing with a physical button press. This process prevents malware on your computer from altering transaction details or stealing keys.
Software wallets installed on phones or computers offer more convenience but expose keys to device vulnerabilities. Mobile wallets suit small amounts for everyday spending. Desktop wallets work well for moderate holdings when combined with strong device security. Web wallets accessed through browsers provide maximum convenience but minimum security.
Researching best cryptocurrencies for 2026 includes evaluating wallet options for each asset. Some cryptocurrencies require specific wallet software while others work with multiple platforms. Staying informed through daily crypto news helps you learn about new wallet releases, security updates, and compatibility improvements.
Paper wallets represent an extreme cold storage option where you print private keys and addresses on paper, then delete all digital copies. While offering maximum isolation from online threats, paper wallets require careful handling to prevent physical damage, loss, or unauthorized viewing. They work best for long-term storage of assets you don’t plan to access frequently.
Multi-signature wallets require multiple private keys to authorize transactions, distributing control across several devices or people. This approach prevents single points of failure and works well for shared funds, business accounts, or high-value holdings where additional security justifies the complexity.
Explore more in blockchain and crypto innovations
Securing your digital assets represents just the beginning of your cryptocurrency journey. DailyTouch provides comprehensive resources to deepen your understanding of blockchain technology, market trends, and emerging innovations shaping the crypto landscape in 2026.
Our blockchain explained guide breaks down complex concepts into clear, actionable knowledge. Whether you’re curious about consensus mechanisms, smart contracts, or decentralized applications, these resources build on the security foundation you’ve established here.
Explore blockchain innovation advances to understand how new technologies improve security, scalability, and real-world utility. Learn how businesses integrate blockchain through our trends analysis, discovering practical applications beyond cryptocurrency trading. These insights help you make informed decisions about which projects and platforms deserve your trust and investment.
FAQ
What is the most secure way to store my crypto private keys?
Hardware wallets provide the highest security by storing private keys on offline devices that never expose them to internet-connected computers. For maximum protection, combine hardware wallets with metal backup plates for seed phrases stored in physically secure locations like safes.
How does two-factor authentication improve crypto account security?
Two-factor authentication requires a second verification method beyond your password, preventing account access even if attackers steal your credentials. Authenticator apps or hardware keys offer stronger protection than SMS codes, which remain vulnerable to SIM swapping attacks.
Can I recover my crypto if I lose my recovery seed phrase?
No, losing your seed phrase without other backup methods means permanent loss of access to funds in personal wallets. This irreversibility emphasizes why secure physical backup of recovery phrases is critical. Custodial wallets may offer account recovery through identity verification, but you sacrifice control for this convenience.
Are custodial wallets safer than personal wallets?
Custodial wallets trade security control for convenience, trusting platforms to protect your assets. Personal wallets give you complete control but require disciplined security practices. Neither is universally safer; the right choice depends on your technical ability, portfolio size, and willingness to manage security responsibilities.
How can I spot phishing attempts targeting my crypto accounts?
Phishing sites use URLs with subtle misspellings, lack HTTPS encryption, or appear through suspicious links in emails and messages. Legitimate platforms never request seed phrases, private keys, or passwords through any communication channel. Always type URLs manually and verify sender authenticity before clicking links or providing information.
Recommended
- Why Use Blockchain in 2026: Unlock $16T Asset Market
- Master blockchain data privacy in 2026: 94.7% accuracy
- How to interpret crypto news for smarter investing in 2026
- How to Invest in Crypto: 30% Returns with Safe Strategies